Introduction
Hadolint is an open-source tool that will help you ensure that all the Dockerfiles you create follow all the Dockerfile best practices available in an automated way. Hadolint, as the number already suggested, is a linter tool and, because of that, can also help you to teach you all these best practices when creating Dockerfiles yourself. We already talked about it the optimization of container image size, but today we are going to try to cover it more in-depth.
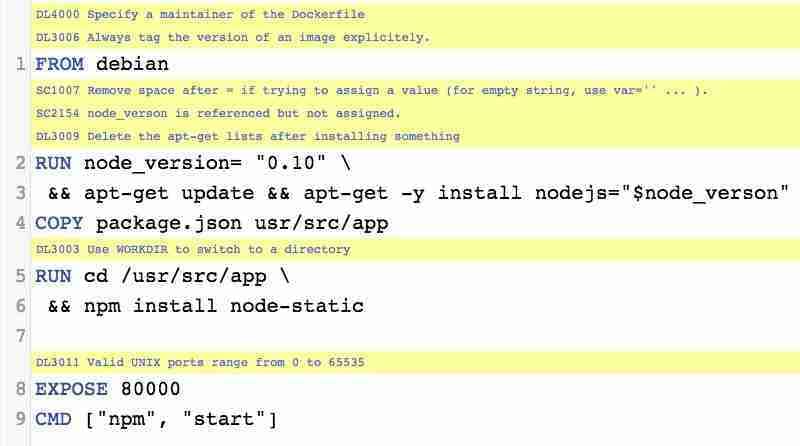
Hadolint is a smaller tool written in Haskell that parses the Dockerfile into an AST and performs rules on top of the AST. It stands on the shoulders of ShellCheck to lint the Bash code inside RUN instructions, as shown in the picture below:
There are several ways to run the tool, depending on what you try to achieve, and we will talk a little bit about the different options.
Running it as a standalone tool
This is the first way we can run it as a complete standalone tool that you can download from here , and it will need to do the following command.
hadolint <Dockerfile path>It will run against it and show any issue that is found, as you can see in the picture below:
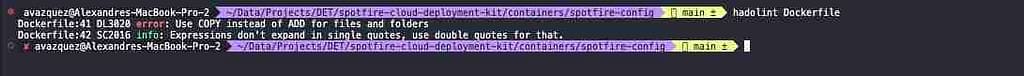
For each of the issues found, it will show the line where the problem is detected, the code of the Dockerfile best practice check that is being performed (DL3020), the severity of the check (error, warn, info, and so on), and the description of the issue.
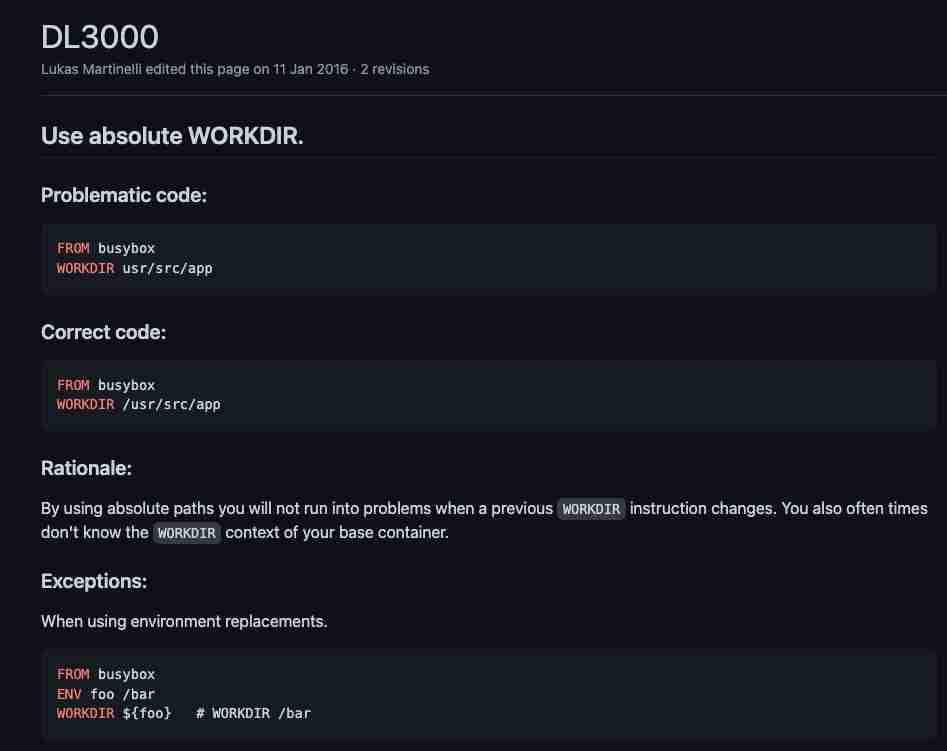
To see all the rules that are being executed, you can check them in the GitHub Wiki , and all of them are based on the Dockerfile best practices published directly from Docker on its official web page here.
For each of them, you will find a specific wiki page with all the information you need about the issue and why this is something that should be changed, and how it should be changed, as you can see in the picture below:
Ignore Rules Capability
You can ignore some rules if you don’t want them to be applied because there are some false-positive or just because the checks are not aligned with the Dockerfile best practices used in your organization. To do that, you can include an —ignore parameter with the rule to be applied:
hadolint --ignore DL3003 --ignore DL3006 <Dockerfile>Running it as Docker Container
Also, the tool is available as a Docker container in the following repos:
docker pull hadolint/hadolint
# OR
docker pull ghcr.io/hadolint/hadolintAnd this will help you to be introduced to your Continuous Integration and Continuous Deployment or just to be used in your local environment if you prefer not to install software locally.
Running it inside VS Code
Like many linters, it is essential to have it close to your development environment; this time is nothing different. We would like to have the Dockerfile best practice relative to the editor while we are typing for two main reasons:
- As soon as you get the issue, you will fix it faster so the code always will have better quality
- As soon as you know of the issue, you will not make it again in newer developments.
You will have a Hadolint as part of the Extensions: Marketplace, and you can install it:
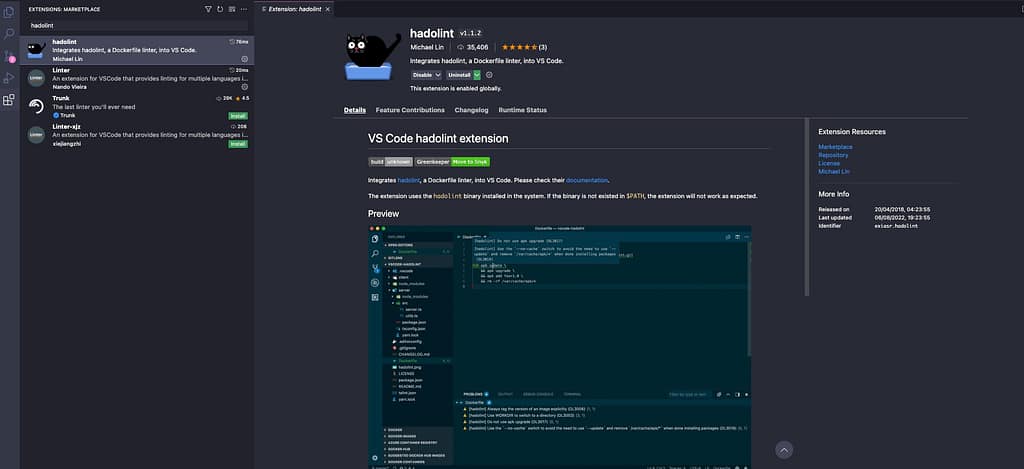
Once you have that done, each time you open a Dockerfile, you will validate against all these Dockerfile best practices, and it will show the issues detected in the Problems view, as you can see in the picture below:
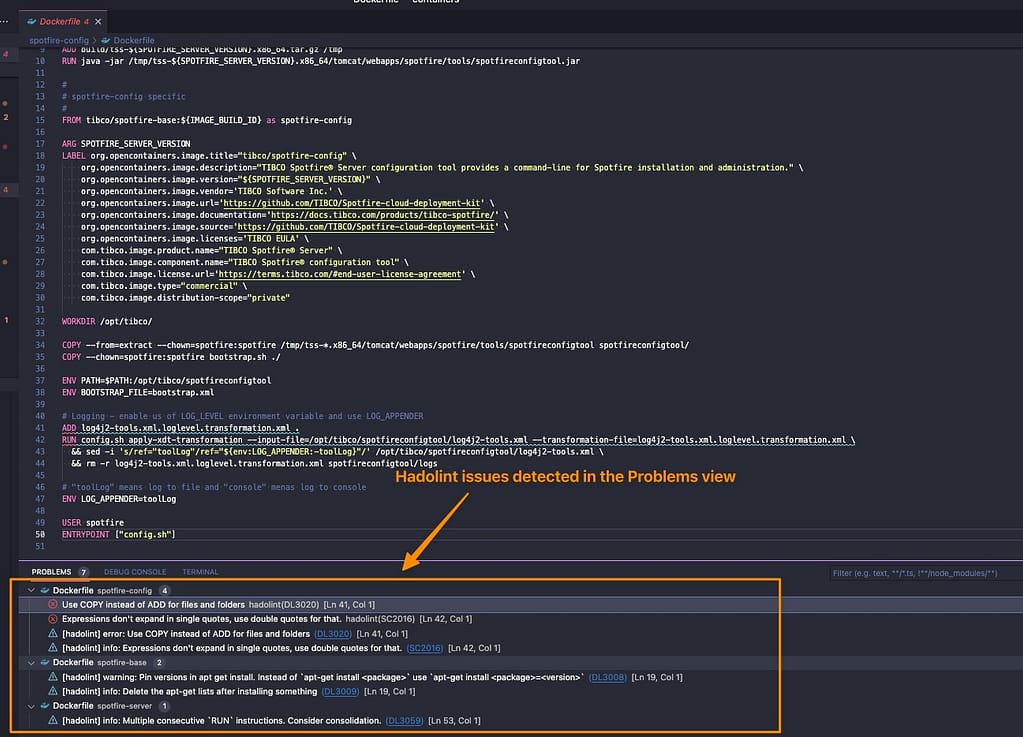
And those issues will be re-evaluated as soon as you modify and save the Dockerfile again, so you will always see the live version of the problem detected against the Dockerfile best practices.

